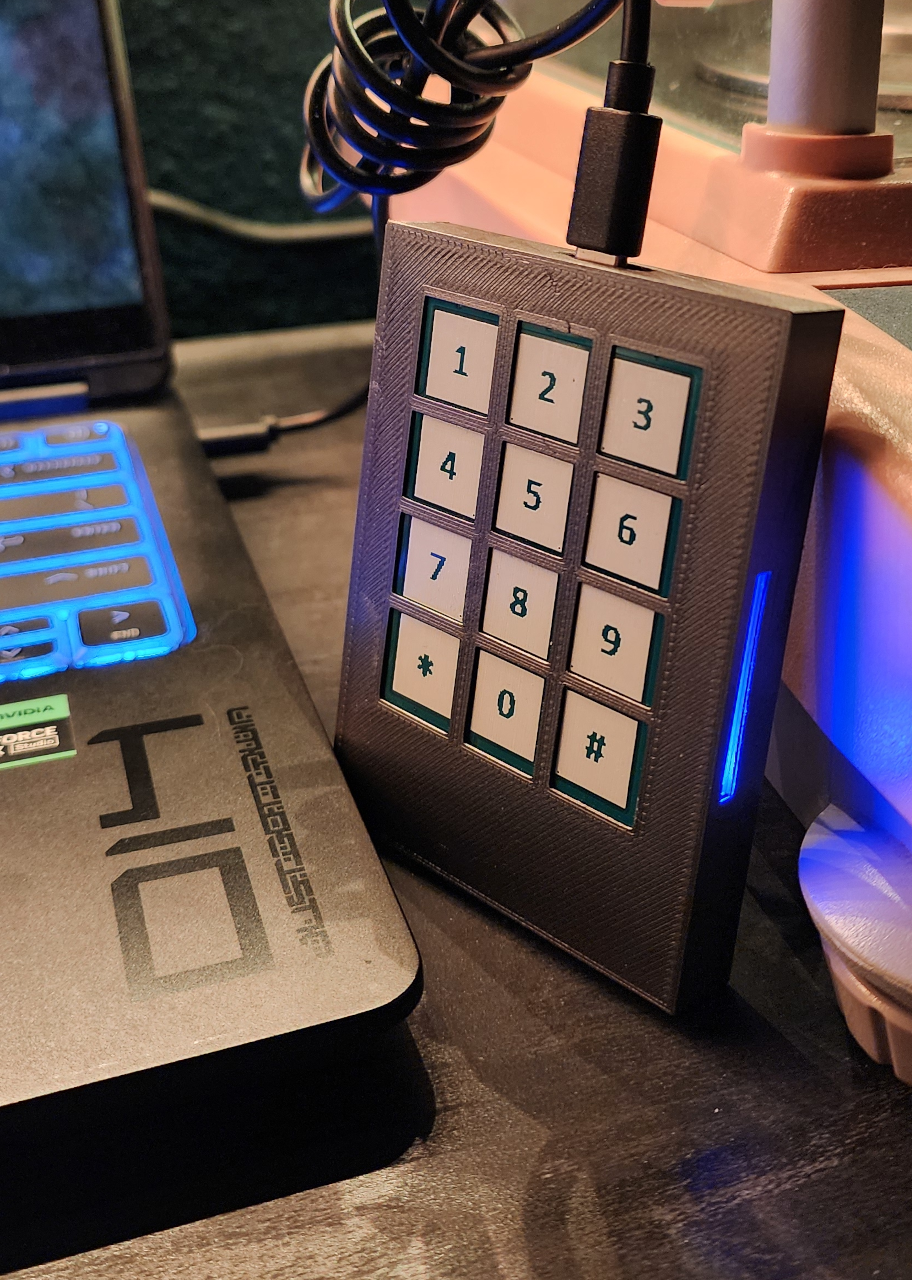
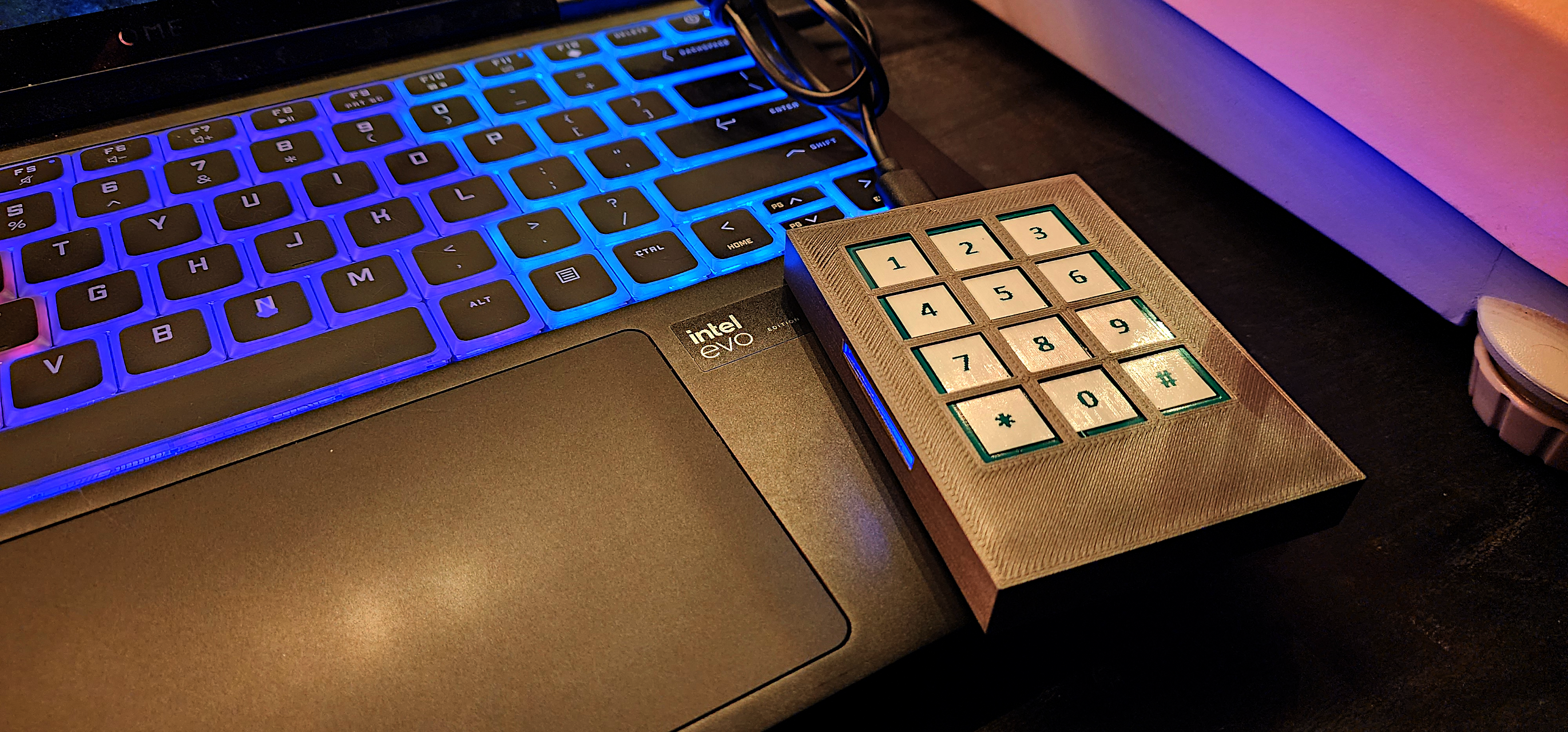
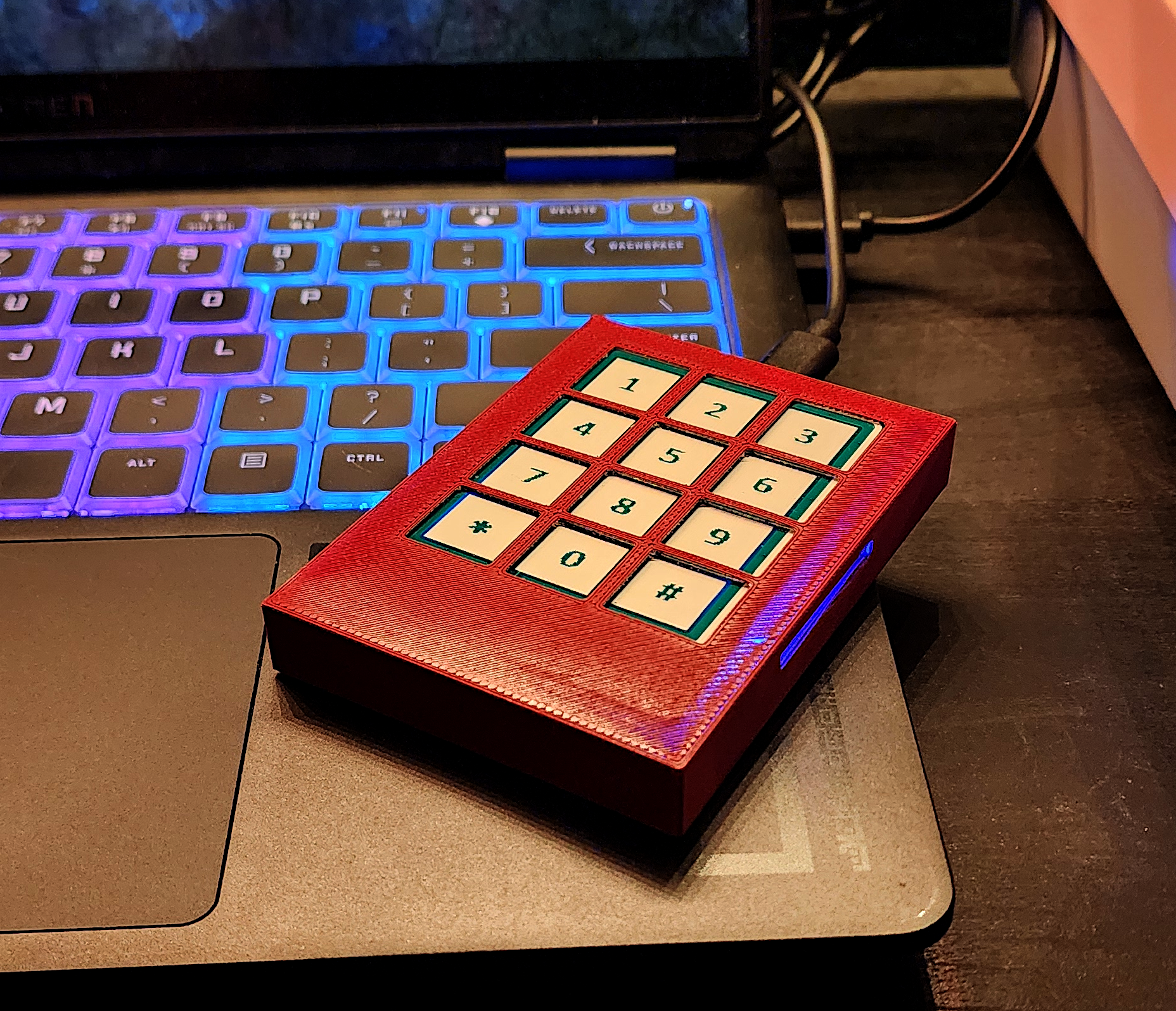
Most people create passwords they can actually remember — and that’s the problem. If you can remember it, a computer can probably crack it. The Cipherpod solves this by taking something simple (a PIN and a small tag on your keychain) and turning it into a password so complex that even powerful computers can’t break it… ever.
How hard is a password to crack?
Password strength is measured in “bits” — the higher the number, the harder it is to crack. Here’s how that breaks down in the real world:
- Home use or older systems: 8 characters or fewer (30-50 bits)
- Early 2000s business standard: 6-10 characters (35-59 bits)
- Modern workplace requirement: 10-14 characters (60-79 bits)
- Finance, healthcare, and regulated industries: 15+ characters (~98 bits)
- Federal government and contractors: 18+ characters (~118 bits)
- “Future-proof” / top secret level: 20+ characters — exceeds every current standard
Most passwords people create from memory — even longer phrases — fall around 40 bits or below. That’s not enough for most modern requirements.
How the Cipherpod helps
The Cipherpod combines two things you already have: a PIN you remember and a small RFID tag (like the chip on a hotel room key or key fob). Together, they generate a random, long, complex password that meets or beats every security policy out there.
When you need a new password, you just change one digit of your PIN. The result is a completely different password that looks nothing like the old one.
It also works in situations where a traditional password manager simply can’t, such as in these examples:
Use at Work
Most workplaces require a password better than “MyPass1!”, and when you find a good password (or passphrase) you have to change it regularly anyway. Using the Cipherpod means you only have to remember a 4 digit pin to have an above-industry-standard password, and changing the password just means changing even 1 character in your pin to generate a completely different password.
In non-audited, average environments, you could even write your PIN on a Post-It note and put in under your keyboard or right on your screen without breaking password policy!
Use at Home
Most people don’t even have passwords on their home computers, but this leaves your computer susceptible to a myriad of risks that would make your personal and private computer easy pickings for an attacker. Using a Cipherpod makes having a strong login password on your home computer and yet is very easy and quick to use.
In homes with children and administrative controls to limit screen time, it’s increasingly important to have a strong password the children can’t guess, and the older they are the more persistent they can be. The parent can leave a Cipherpod on their desk connected to the computer, and even if the child can guess the PIN the parent might use they can’t get the RFID keyfob on their keyring while the parent is out of the house, making use of the computer impossible. This would be true for desktops, laptops, modems and any digital device requiring a password.
Time controlled access also becomes possible – limiting screen time until a parent comes home means the children can’t log in without the RFID fob on their keyring. Parents don’t have to worry about hiding the password as they type it; they could post the PIN on the refrigerator if they wanted to.
Full-Disk Encryption
Whole-drive encryption requires a password because there’s no network yet, no server, no cloud resources to check the password. On such a machine there’s no point employing strong, 256-bit encryption when your password is “toughasnails123” (50-60 bit using dictionary words – this can be cracked in less than 10 minutes on any laptop). The Cipherpod can easily generate a 256-bit password so long that the user would never be able to remember and yet will never mistype it.
Schools and Use With Students
Computer labs in educational facilities often have a username and password assigned to every student, but very few students select decent passwords, and this can lead to students using other student’s accounts and blaming them for illicit activity, these student accounts posing a risk to the facility or worse. Providing a Cipherpod to students means they only have to remember 4 numbers and bring their student ID/access card to the computer lab. It becomes impossible for another student to commandeer their account even if they watch them enter their PIN (“shoulder surfing”).
Remote Support & Elderly Use
In the example of providing remote support to a family member, the Cipherpod can really shine. Elderly users never consider how insecure it is to send a password over SMS text or write it on a Post-It note, and it would be almost impossible for them to set different passwords for every site they use which is important nowadays. Just general use of a Cipherpod would ensure their banking, insurance and other web portals have powerful passwords while the user only has to write down a PIN, and it makes changing their passwords trivial in the event of compromise by malware.
Family members can have multiple Cipherpods keyed the same way and a physical copy of the same RFID token, so the elderly user simply has to share a PIN – even over SMS text – and the family members can log into email, banking and insurance sites on their behalf.
There are many tragic cases of home care staff logging into elderly users’ computers while they’re away, having helped them with their computers at some point. It is impossible to log into the computer while the elderly person is away since their RFID key is on their keychain.
Password Manager Compromise
There are many instances where cloud-based password manager providers have been compromised, and people’s whole database of passwords has been leaked to the Internet underground. Using a Cipherpod, users only need to use a password manager to retain their PIN for a given website, and if that PIN is leaked it still doesn’t leak their actual password (for example, in the password manager for your bank account, you write “cpod 56473”).
Compliance and Audited High-Security Environments
Regulated industries that require complex passwords and frequent rotation benefit from Cipherpod’s deterministic generation. Organizations can meet HIPAA, SOX and all government security standards without user training overhead or password storage risks.
Cipherpods generate 8 character complex passwords just as easily as 256-bit credentials, so users can easily produce login passwords that are compliant with even the most strict password policies, and change them very easily.
Dual-Person Authentication and Authorization
With a Cipherpod connected to a high-security computer, both a PIN and RFID tag are required to make it generate the strong login password. An individual with the PIN and another individual with the RFID tag would be required to access this computer.
This can be useful in banking, finance, trade and protecting high security keys such as Certificate Authority encryption keys. Emergency Broadcast systems would require both the technician and supervisor authorization. In Legal and Compliance environments, a digital evidence locker could only be accessed when both the attorney and forensics technician are present. Information for accounts and site credentials inherited after death could only be accessed when the attorney provides the RFID tag and a family member has the PIN to the password manager software.
Crypto-Currency Cold Storage
There are many unfortunate instances of YouTube influencers and Internet personalities being physically attacked for their Bitcoin wallets or account access. Offline wallets can be protected with an RFID key being kept in a safe offsite and the individual retaining the PIN, making compromise impossible no matter what the circumstances.
Protection Of A Device During Travel
Lawyers, Journalists and others often have to travel internationally, and the digital devices they bring with them (or have checked in their luggage) are prime targets for theft or coercion. Even just having a laptop stolen in a terminal can be a serious situation for anybody.
The laptop owner has plausible deniability by shipping a copy of the RFID key to the destination ahead of time and leaving the original key at home. This makes logging into the device mid-transit impossible even for the device owner, who can give up the Cipherpod and PIN without compromising their computer.
Enforce Local, Physically-Present Access
On high-security machines with uniquely-keyed Cipherpod Black units, the locally-connected Cipherpod must be interacted with to type the PIN and read the authorized RFID tag. The PIN cannot be typed remotely and of course the physical token must be read by the device before it would transmit the actual password into the machine.